This article applies to:
- MailMarshal SEG Service Provider Edition
- Microsoft Azure Active Directory
Question:
- How can SPE user information be imported from Azure AD?
Procedure:
The Connector Agent is an optional module of SPE that allows you to retrieve information about local user groups and email addresses from an Active Directory server or LDAP server, for use in email filtering policy.
You can use the Connector Agent with Azure AD.
- Note: In current versions of SPE, customers can retrieve Azure/Entra directory information directly, using the Entra Connector. This is a much quicker and more robust option. See customer facing documentation. Basic information on the required setup in Entra is found in LevelBlue Knowledgebase article Q21246.
If a customer has a workstation or server available on premises that is a domain member, they can install and configure the Connector Agent for Azure AD in the same way as for a premises AD installation.
- Note: For customer-focused basic instructions about how to download, install, and configure the Connector Agent, refer to the End User Guide provided with SPE.
The customer or Service Provider can also use the Connector Agent to synchronize information from Azure AD using LDAPS.
- Note: The Service Provider can host Connector Agent service for multiple customers with a single installation. See article Q14972.
To use the Connector Agent with Azure AD LDAPS:
- Configure Secure LDAP (LDAPS) in Azure AD Domain Services. See the Microsoft documentation for this task.
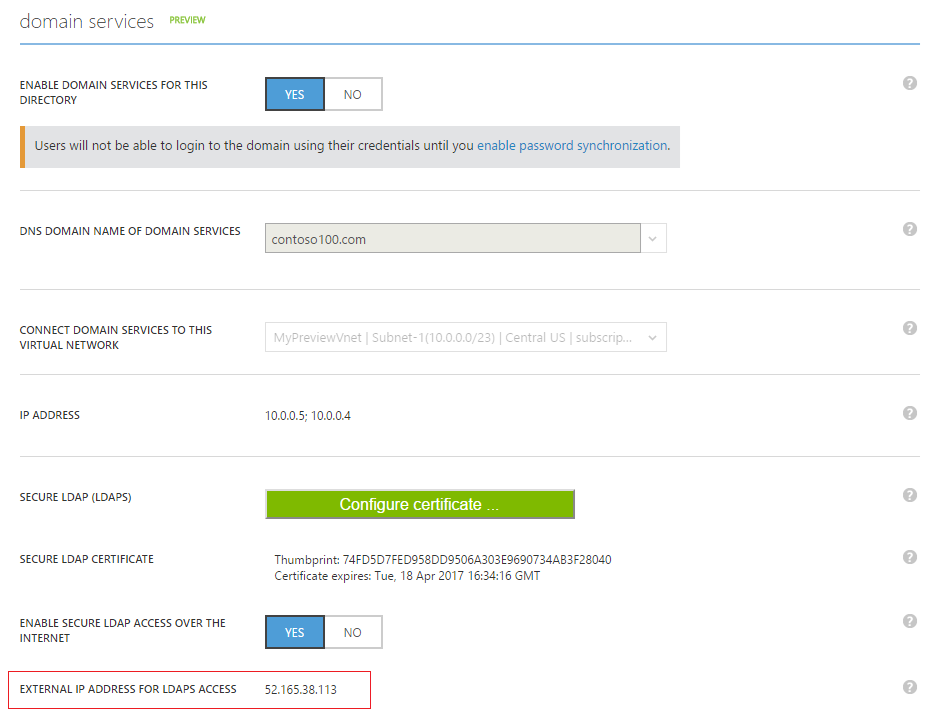
- Once secure LDAP access to a managed domain over the internet is successfully enabled, the Azure AD Domain Services management site shows the external IP address that can be used to access the directory over LDAPS in the field EXTERNAL IP ADDRESS FOR LDAPS ACCESS.
- Install the Connector Agent on any computer that has Internet access (HTTPS access to the SPE Customer Console, and port 636 for LDAPS access to the Azure LDAPS IP address).
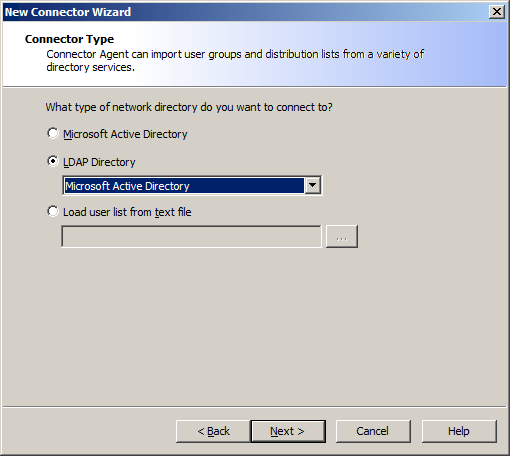
- Create a new connector, and specify a LDAP directory of type “Microsoft Active Directory”.
- Enter the Azure LDAPS IP address. Specify port 636 and select Connect using SSL. Enter logon credentials.
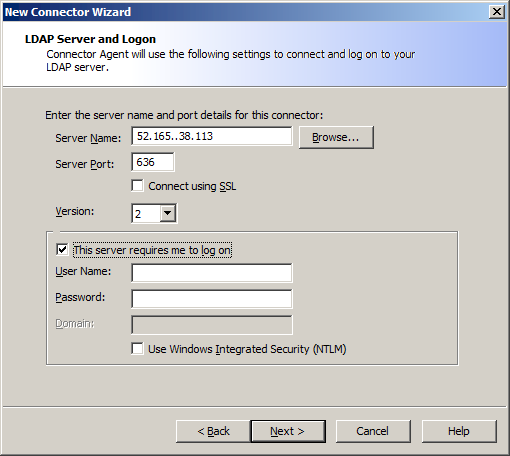
- Click Next. The Agent tests the connection.
- When the connection is successfully tested, continue the Wizard as described in the End User Guide.
- When the connector has been successfully created, you can proceed to select groups for synchronization.
