This article applies to:
Question:
- iTunes radio stations do not function properly with default security policy. With few changes listed below you could allow these contents through SWG proxy.
Procedure:
First, it is possible that current security policy blocks initial requests for iTunes radio stations. All iTunes radio stations are being launched as PLS file, with further connection to a remote server.
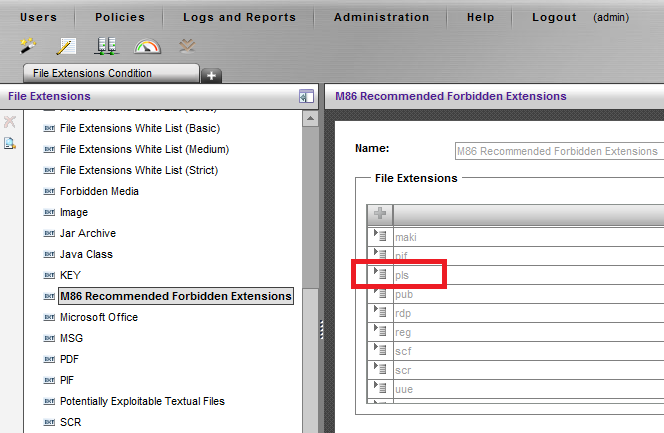
This file extension is listed among M86 Recommended Forbidden File Extensions.
Review SWG web logs to validate if there are any blocks of Block Forbidden Extensions rule.
If there are no blocks of this kind, continue with below article to modify the settings to allow iTunes radio station contents.
If there are blocks of PLS file extension, make sure your security policy is set to allow PLS files.
iTunes radio stations are streaming audio contents over the web, and it have to be allowed to stream contents in the same fashion that SWG allows video streaming.
Refer to the Allow Streaming rule in your security policy and make sure that Audio File True Content Type is checked as shown below:
It is also possible that some audio streaming would be using a custom Content-Type that would have to be allowed in a different way.
1. First, find out what these Content-Types are. This could be found in a network capture collected when a proxy was requested to deliver these streams.
Refer to Notes section below to find a KB on how to collect tcpdump network captures on a SWG device:
Below example shows typical responses from the web server:
Note that SWG identifies above Content-Types as Audio File True Content Types, here it is only being used for demonstration purposes.
2. Navigate to the GUI section: Policy -> Condition Settings -> Header Fields, and create new Header Fields list, Audio Streaming, as shown below:
3. Edit this Header Fields list to include the following two entries for above Content-Types:
4. Navigate to the GUI section: Policy -> Security -> Advanced and review current security policy.
Create new rule to Allow Streaming Contents based on Content-Types, and refer to the Header Fields list created in step 3:
Just as with default Allow Streaming rule in M86 Security policies, make sure that this new rule is set with Advanced Action to Bypass Scanning and is located on top of the policy:
Save and commit the changes.
Notes:
KB - How to run tcpdump trace on SWG device - https://support.trustwave.com/kb/KnowledgebaseArticle14333.aspx