SWG comes with a number of commands designed to assist administrators with troubleshooting. The tcpdump command can be used to collect a network trace for detailed review.
The article below provides step-by-step instructions on how to run this command and how to copy traces from SWG to a local computer.
This task requires SSH access to SWG - could be All-In-One/Policy Server/Scanning Server.
1. Login to the limited shell interface using an SSH client (PuTTY, a free SSH client for Windows is depicted in the screenshots below).
2. Run the tcpdump command:
3. The limited shell's implementation of tcpdump supports filters to reduce the number of packets to be collected, similar to the filters available on the Linux tcpdump command (e.g., port 8080, host 192.168.1.29, etc.).
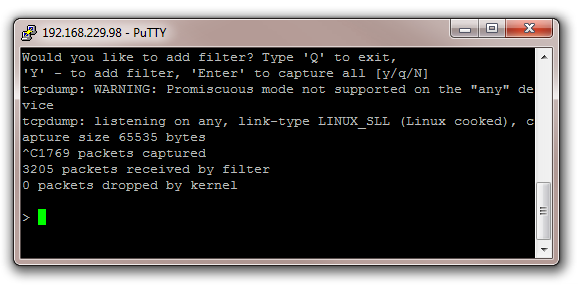
To record all traffic without a filter, press Enter to start the process:
4. Press 'Ctrl C' to stop the trace. Please note that the SSH session might time out and close when you stop the trace, depending on the time this command was running.
This however will not affect the output file - it will collect all relevant packets up to the moment when the trace was stopped.
SWG rotates the output file every 100 MB, so if the trace was running for a long period of time multiple files should be expected.
5. Now it is necessary to retrieve the trace file(s) from SWG for further review. This is done using SFTP (a method for transferring files via SSH). The screenshots below depict using FileZilla (a free SFTP client for Windows) for this purpose.
In addition to specifying the host (the IP or name of the SWG), be sure to indicate the following parameters:
Port: 22
Server Type / Protocol: SFTP
Username: support
Password: use the same password that is used for the limited shell's admin account
Once the connection is established, the support home directory will load:
6. Navigate to the /support/tcpdump/ directory to copy the trace file(s) to your local file system:
Notes:
Any other tool supporting SFTP connections could be used for this purpose. SWG has been tested with FileZilla and WinSCP.
Filters (step 3), examples:
not port 22 (to exclude the ssh connection)
host 192.168.16.13 or host 192.168.16.241 and not port 22 (two hosts, no ssh traffic)
host 192.168.16.13 and port 8080 (only http traffic on a specific client)
