This article applies to:
- Trustwave MailMarshal (SEG)
Question:
- Can MailMarshal modify the email message body?
- How can I remove active links or other material from an email message?
Reply:
MailMarshal does not provide a dedicated rule action to edit email message bodies. You can use an External Command to make changes.
Be aware that External Commands run slowly compared to other rule actions, because they require an external program to load for each usage.
- You can minimize use of the external commands by identifying the bodies that require rewriting using TextCensor scripts or other rule conditions.
- If you plan to use External Commands for a large number of items, carefully monitor email throughput.
You can use any executable that runs from the command line and accepts an absolute path for the file to be processed. To avoid unnecessary repacking of email messages, the executable should return different numeric exit codes for "change made" or "no change made".
The example in this article uses a simple open source text replacement tool, "Find And Replace Text" (FART). See the Related Links section below for download and documentation.
- For a Regular Expression option see the Notes at the end of the article.
This article assumes familiarity with the SEG configuration interface.
The ideas and scripts in this article have been reviewed for accuracy. External executables and scripts are not covered by Trustwave support. Customers use these items at their own discretion.
Procedure:
To set up a rule for text replacement:
- Create an External Command (Policy Elements > External Commands)
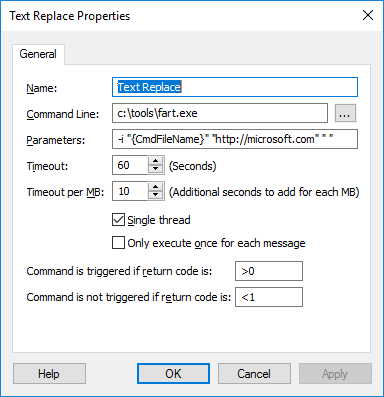
- Command Path: Enter the tool location. The tool must exist in this location on all processing servers.
- Parameters:
- -i indicates case insensitive
- Use "{CmdfileName}" (including quotes) to refer to the file to be processed. SEG will update this variable with the file location.
- The next two parameters are the string to find and the replacement. In the example, the URL http://microsoft.com is replaced with a space. (If you enter an empty string "" FART will not do any replacement.)
- When choosing what to find and replace, be aware that the script will apply to HTML and plain text email bodies. HTML tags are part of the text. A Regular Expression search might be useful to ignore tags (see Notes below).
- Single Thread must be selected.
- Only execute once should NOT be selected. A message can have more than one body part.
- Set Command is triggered to >0 and Command is not triggered to <1
- Save the command.
- Create a rule to apply the command
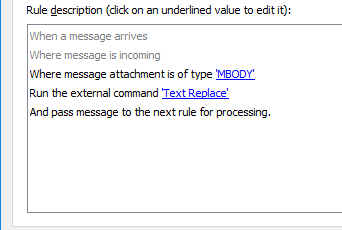
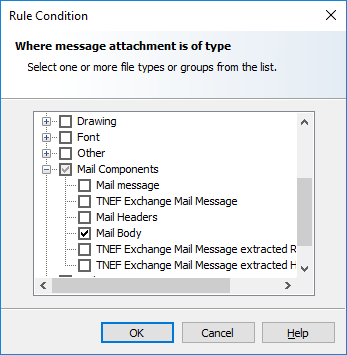
- Choose Message attachment type Mail Body (MBODY) to apply the command only to message body parts.
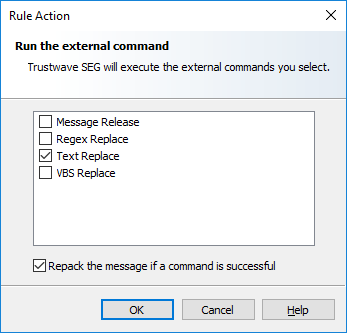
- Choose Run the external command and select the command you created. Be sure that Repack the message is selected.
- Enable and save the rule, and test. The Content Analysis log will be similar to the below:
04532 13:34:33.083 001 Requesting Action <Content:Policy Management (Inbound):Text Replace:Text Replace,repack> be run04532 13:34:33.090 001 TRIGGERED command <"c:\tools\fart.exe" -i "C:\Program Files\Trustwave\Secure Email Gateway\Unpacking\T1\U2\Plain.txt" "http://www.microsoft.com" "">.
Result= 1 after 7 millisecs04532 13:34:33.090 001 Repacking message after external command succeeded.
Notes:
Trustwave is not currently aware of a simple executable that provides Regular Expression replacement. For advanced users, the attached zip file (replace-regex.zip) contains a sample Visual Basic script that can be used in an external command. Caution: This script executes somewhat more slowly than FART.
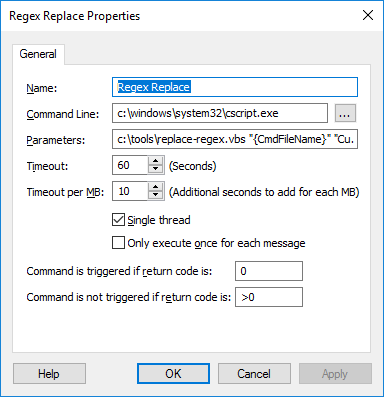
- Command Path: Refers to CScript (the Windows VBS command line script interpreter).
- Parameters: enter a string similar to
c:\tools\replace-regex.vbs "{CmdFileName}" "http.+://.*?\.microsoft\.com" "" - Enter the path to the script. The script must exist in this location on all processing servers.
- In the image it is assumed you have put the script in the "Config" subfolder of the MailMarshal installation on the Array Manager. It will be copied to "NodeConfig" on all servers.
- The variable {Install} expands to the MailMarshal installation location.
- Use "{CmdfileName}" (including quotes) to refer to the file to be processed. MailMarshal will update this variable with the file location.
- The next two parameters are the Regular Expression string to find and the replacement. For example:
http.+://.*?\.microsoft\.com matches http or https and any subdomain/server of microsoft.com - You can use an empty replacement string to delete the value found.
- This script as provided is case sensitive. You can edit the script and add the IgnoreCase flag for the VBS RegEx object.
- Single Thread must be selected.
- Only execute once should NOT be selected. A message can have more than one body part.
- Set Command is triggered to 0 and Command is not triggered to >0