This article applies to:
Question:
- What is Security Reporter Evaluation Mode?
- What data is available for reporting in Evaluation Mode?
- How do I request an extension or registration for a SR in Evaluation Mode?
Information:
By default, the SR is set to evaluation mode. Evaluation mode limits the available reports to the most recent 14 days of data. Data for earlier dates is stored but cannot be reported on. Evaluation mode is only available for a limited time.
This article explains how to request an extension of evaluation, or to register the SR.
C.1 Report Manager Banner
In evaluation mode, the Report Manager banner displays ‘EVALUATION MODE’ beneath the Security Reporter name/link.
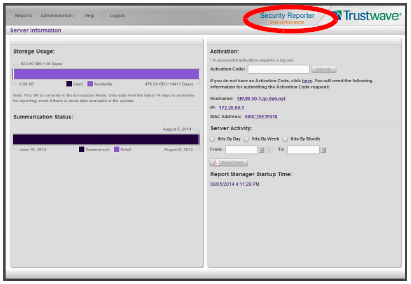
Hover over the ‘EVALUATION MODE’ link to display a definition of ‘Evaluation Mode’. Click this link to launch the SR Server Information screen.
Note: The Server Information screen is available to all administrators through this link (the Administration menu item is visible only to Global Administrators).
In Evaluation Mode, the Storage Usage section of the Server Information screen includes a note about the data available for reporting.
Server Information Screen
For an SR unit currently in evaluation mode, the Server Information screen includes the Activation section, as shown above. You have the option to either use the SR in the evaluation mode, or to change the evaluation mode in one of two ways: by extending the evaluation period, or by registering the SR so that it can be used in the registered mode.
Change the Evaluation Mode
When the designated evaluation period has expired or is about to expire, you can request an extension to your evaluation period, or register the unit and use it in the registered mode.
- In the Activation section of the sever information screen, you will find the Hostname of the Server, IP address, and MAC Address (hardware address of the LAN1 network interface).
- In the message “If you do not have an Activation Code, click here.”, click the link ‘here’ to open the Product Activation page at the Trustwave Web site.
- In this Web page:
- Enter your following information: Contact Details, Company Information, and Security Reporter Information.
- Choose the Activation Type: “Evaluation Extension” or “Full Activation.”
- Click Send Information. Trustwave will review the request and issue you an activation code (subject to contractual considerations).
- When you receive the code, return to the Activation Page and enter the activation code in the Activation Code field.
- Click Activate to display the confirmation message in the Activation Page pop-up box:
- If you have extended the evaluation period for the unit, the following message displays: “It is now in evaluation mode (‘X’ days)!” where ‘X’ represents the number of days in the new evaluation period.
- If you have registered the unit, the following message displays: “Your box has been activated!”
Notes:
This information is copied from the Security Reporter Administrator Guide. For the full Guide and other documentation, see the Security Reporter Documentation page.

