This article applies to:
Question:
- How do I configure SMTP Authentication for Active Directory users?
Procedure:
In current versions of MailMarshal, you can validate SMTP authentication for users against an AD group. In this case you do not need to enter individual accounts in the MailMarshal Accounts.
This functionality is implemented on the email processing servers.
To use this functionality, the email processing servers must be joined to Active Directory and the network ports required by AD must be open for the email processing servers.
This functionality does NOT use the AD connector configured in MailMarshal.
To configure this functionality:
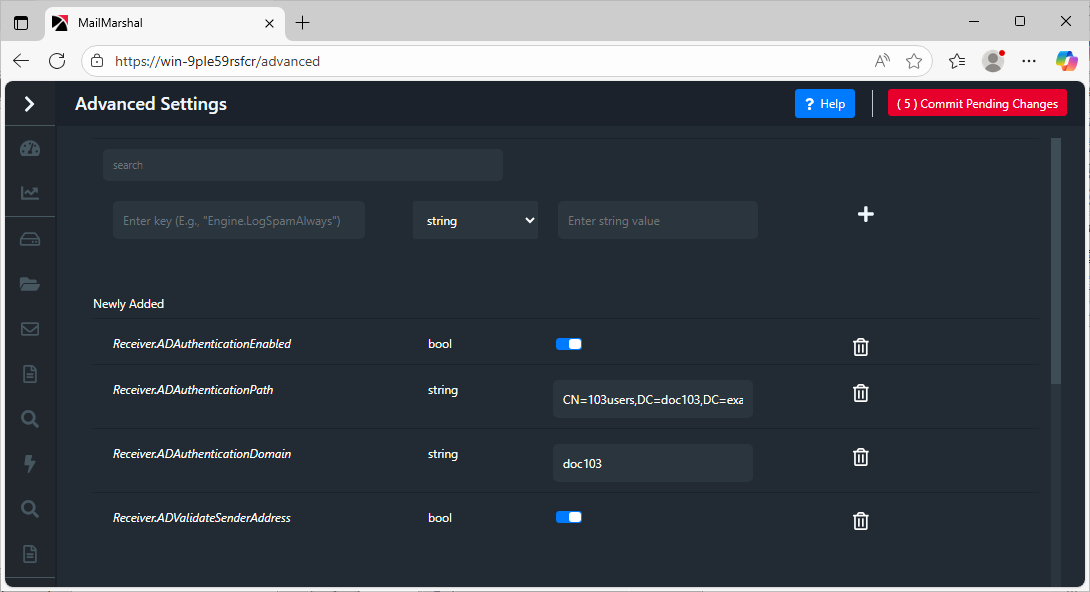
- In MailMarshal 10.0 and above, open the Management Console and navigate to Advanced Settings. Add the following value entries:
- Receiver.ADAuthenticationEnabled (Boolean)
- Receiver.ADAuthenticationPath (String)
- Value: The CASE SENSITIVE full DN path of the user group such as
CN=Auth Users,DC=test,DC=com
- Receiver.ADAuthenticationDomain (String)
- Value: The name of the AD domain to use if a domain is not provided when authenticating (in pre-2000 domain format)
- Receiver.ADValidateSenderAddress (Boolean)
- Optional value: if present and set to True (selected), the user email address is validated as described below.
- In MailMarshal 8.X, open the Registry Editor on the Array Manager. Within the base registry key, navigate to \Default\Receiver
- Add the following value entries:
- ADAuthenticationEnabled (DWORD)
- Value: 1 to enable this functionality (0 to disable)
- ADAuthenticationPath (REG_SZ)
- Value: The CASE SENSITIVE full DN path of the user group such as
CN=Auth Users,DC=test,DC=com
- ADAuthenticationDomain (REG_SZ)
- Value: The name of the AD domain to use if a domain is not provided when authenticating (in pre-2000 domain format)
- ADValidateSenderAddress (DWORD)
- Optional value: if present and set to 1, the user email address is validated as described below.
- Save your registry settings or configuration settings.
- Commit the configuration changes and restart the MailMarshal Receiver service on each node.
Operation:
To use this function:
- Users must be members of a specific group (not just an OU)
- Passwords MUST be sent in clear text to use this feature (AUTH PLAIN or AUTH LOGIN).
- To improve security, use authentication over TLS.
If ADAuthenticationEnabled is set, the following process occurs for each authentication attempt:
- Check if the requested username includes a \ character. If not, use the domain name specified under ADAuthenticationDomain
- Note: usernames in User@Domain format will not work.
- Check that the domain exists and the user can be found in the domain. If this step fails, go to step 5 below.
- Get the groups the user is a member of, and compare the groups returned to the ADAuthenticationPath value.
- If the user is a member of the group, authenticate against the domain and return success or failure depending on the result.
- If ADValidateSenderAddress is enabled, the Return Path of the message must be an email address in the authenticated sender's list of email addresses from Active Directory.
- Return Path is the MAIL FROM address if present, otherwise the header From: or Sender: address.
- If the user is not a member of the group, but the account is found in the accounts table in MailMarshal, then authenticate against the password set in MailMarshal and return success or failure depending on the result.
- If the account is entered in MailMarshal with a blank password, authenticate against the domain.
Notes
Take due care when editing the Registry.