This article applies to:
Question:
- Is it possible to use different upstream proxies based on conditions?
- How do I use the upstream proxy policy?
Procedure:
In order to forward requests to different upstream proxies, basically three steps are necessary:
- Define conditions
- Create an upstream proxy "Object"
- Assign this upstream proxy to the scanner(s)
The best practice is to perform the steps in the order that they are listed above. As an example, an administrator might want to use a specific upstream proxy for an individual URL. The administrator would follow the steps below.
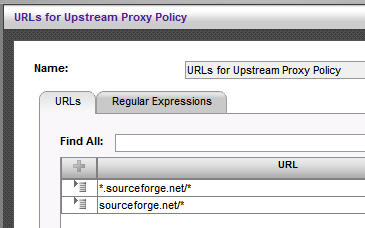
1. Create a URL list accordingly:
2. Create a "Upstream Proxy Object":
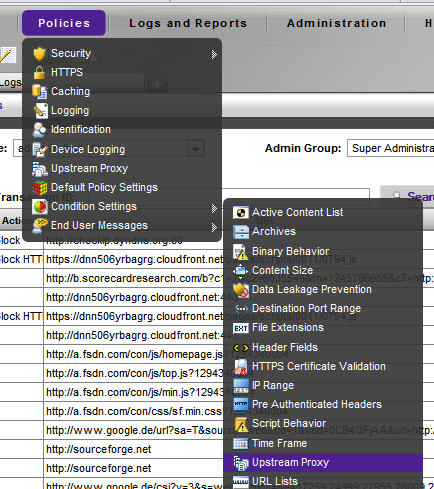
2.1 Policies > Condition Settings > Upstream Proxy
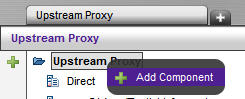
2.2 In order to add a Upstream Proxy, right click [Upstream Proxy]:
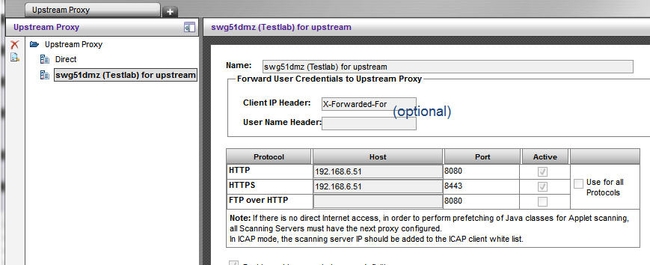
2.3 Define your Upstream Proxy details (IP address, ports, ...):
3. Create the Upstream Proxy policy and assign it to the Scanner(s)
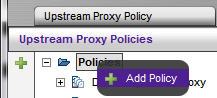
3.1 Under Policies > Upstream Proxy, add a Policy:

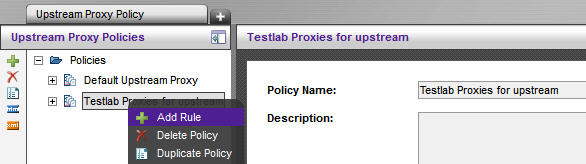
3.2 Add a rule to this policy, in order to use the condition(s) defined in step 1:
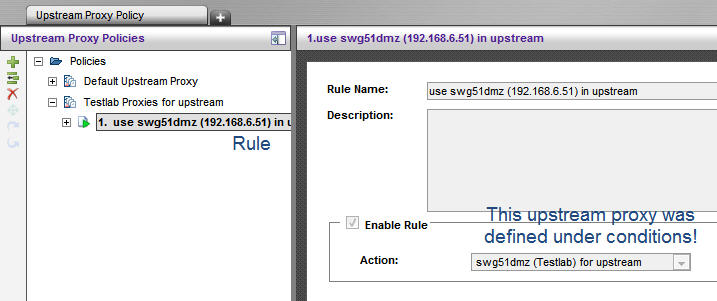
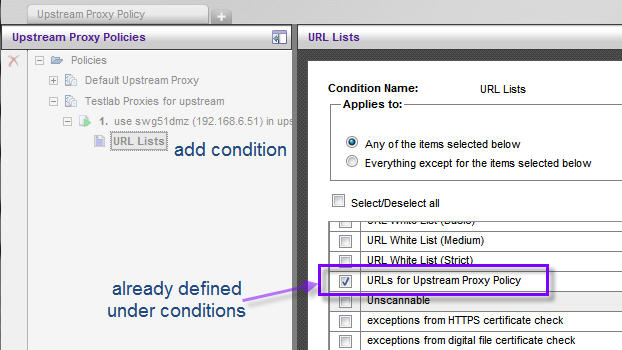
3.3 Add the condition(s)
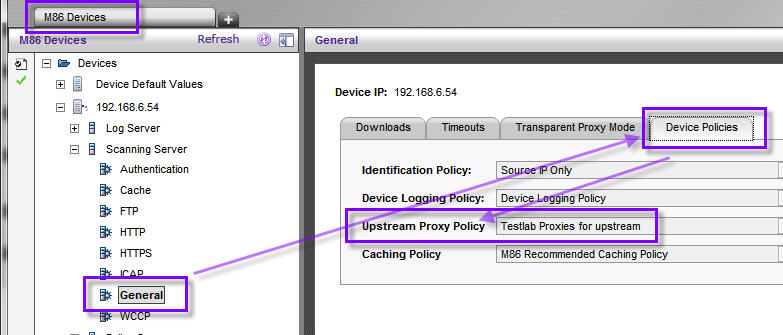
3.4 As a last step, assign this Upstream Policy to your scanner(s); the new Upstream Proxy policy can now be found in a dropdown-list in "Scanner Device Policies":
Notes:
- Upstream Proxy policies can be defined "per scanner", providing the ability to distinguish between local and cloud scanners!
- Security Policies are evaluated regardless of Upstream Proxy Policies; according to your requirements it might be necessary to whitelist client requests accordingly before they are sent to the upstream proxy!
- Of course other conditions, such as header fields or IP range can be used.
- One Upstream Proxy Policy can point to more than one upstream proxy. This does not automatically include Backup Upstream Proxy functionality.
- Important for troubleshooting: When caching is enabled the scanner process connects to the caching server (upstream) and the caching server connects to the "real" configured upstream server. So when looking at traffic captures or logs, this behavior will be seen in the logs/cap files.