This article applies to:
- Marshal Reporting Console 2.5
- Windows Server Update Services (WSUS)
- Windows Server 2008
Question:
- How do I configure the Marshal Reporting Console (MRC) website on a server running WSUS?
- MRC website does not run correctly when WSUS is also installed
Procedure:
Note: In addition to this article, see Q12671 (in particular the instructions on how to disable HTTP Compression).
Marshal Reporting Console is configured by default to use a subfolder of the default website.
Earlier versions of MRC (2.5.2 and below) are also configured to use the default Classic .NET application pool with some configuration changes.
WSUS also makes some changes to default IIS settings.
To allow MRC to coexist with IIS configuration created by the WSUS installation:
- Verify the authentication settings for the MRC web application.
- Verify the application pool settings and create a new application pool if necessary.
Authentication settings
MRC uses Windows authentication to identify users. The MRC installation creates the correct authentication settings by default.
If the MRC web pages return server errors that refer to authentication or authorization, verify these settings.
- On the affected server, open IIS Manager.
- In the left pane menu, expand Sites > Default Web Site. Select the application MarshalReportingConsole.
- Open the item Authentication. If an error window displays, click OK to close it.
- Use the right-click context menu to set the status of the following authentication types:
- Anonymous Authentication: disabled
- Basic Authentication: disabled
- Forms Authentication: disabled
- Windows Authentication: enabled
Note that when you navigate away from this item, the status display is lost. However the settings are made and retained correctly.
Application Pool
MRC version 2.5.3 and above creates and uses a new application pool with the correct settings.
With these versions you should not need to change application pool settings.
You may want to verify that MRC is in fact using its own application pool.
- In the left pane menu, expand Sites > Default Web Site. Select the application MarshalReportingConsole.
- On the Actions menu, click Basic Settings. Check the application pool in use. It should be named "MRC Application Pool."
- If it is necessary to create or edit an application pool, see the instructions below.
Manually creating an application pool
If necessary, you can create a new application pool to allow MRC to coexist with IIS configuration created by the WSUS installation, create a new application pool for MRC.
- On the affected server, open IIS Manager. In the left pane menu, right-click Application Pools and select Add Application Pool.
- On the Add Application Pool window:
- Give the pool a name
- Select .NET framework version: 2.0
- Select Managed pipeline mode: Classic
- Click OK.
- In the left pane menu, select Application Pools. In the right pane, select your new application pool. In the Actions menu, click Advanced Settings.
- Configure the following advanced settings:
- Enable 32-Bit Applications: True
- Identity: NetworkService
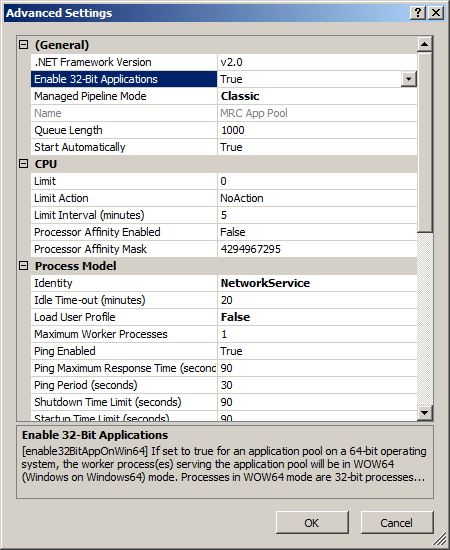
- Click OK.
- In the left pane menu, expand Sites > Default Web Site. Select the application MarshalReportingConsole.
- On the Actions menu, click Basic Settings.
- Select the application pool you created, and then click OK.
